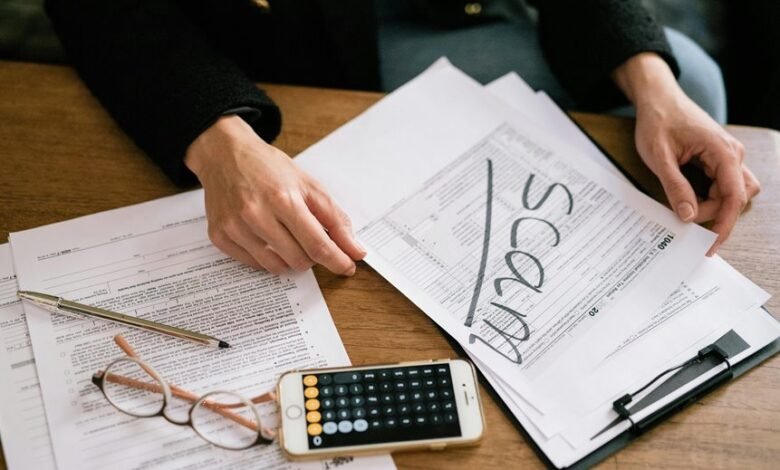
Scam Alert Investigation Hub Phone Number Search Scams Revealing Fraud Detection Searches
The Scam Alert Investigation Hub uses phone-number search patterns to illuminate broader fraud-detection signals. Metrics from caller data are cross-checked against independent databases to identify recurring attacker tactics and credibility cues. The approach emphasizes verification, skepticism, and reproducibility over isolated incidents. Yet the implications remain unsettled: do aggregated signals reliably differentiate risk from noise, and what controls best mitigate exposure without stifling innovation? The tension invites careful scrutiny and continued evaluation.
What Scam-Phone Searches Reveal About Fraud Patterns
Examining scam phone searches reveals consistent patterns in attacker behavior, rather than isolated misdirections. The analysis identifies recurring scam patterns and common fraud indicators, enabling a disciplined appraisal of threat signals. Detachment clarifies how tactics evolve, while skepticism prevents overgeneralization. Freedom-minded readers recognize that structured scrutiny reduces risk, validating methodical vigilance against deceptive calls and inflated credibility claims.
How to Use a Number Search Safely and Effectively
Informed by the patterns identified in scam-phone searches, the safe and effective use of a number search hinges on disciplined methodology and critical evaluation of results.
The approach emphasizes verification, skepticism, and reproducibility: how to verify sources, how to document findings, and how to cross-check against independent databases.
Procedures prioritize evidence, minimize bias, and value methodological transparency over sensational conclusions.
Red Flags You Can Detect From Caller Data and Metadata
Red flags in caller data and metadata are identifiable through disciplined analysis of patterns that persist across multiple signals. The assessment relies on red flags emerging from caller metadata trend analysis, not single events, to avoid spurious conclusions. Privacy considerations temper data enrichment pitfalls, ensuring safeguards while detecting anomalies. Methodical scrutiny preserves autonomy while exposing systemic fraud indicators.
Turning Insights Into Action: Next Steps for Fraud Detection
Turning insights from caller data and metadata into actionable fraud controls requires a structured plan that translates observed red flags into concrete steps. The analysis remains rigorous and skeptical, avoiding overreach while prioritizing autonomy. By identifying patterns and exposing spoofing tactics, organizations can implement targeted controls, audits, and continuous monitoring, ensuring defense strategies adapt without impeding legitimate communication or freedom to innovate.
Conclusion
The analysis demonstrates that phone-number search patterns expose recurring fraud signals when examined as aggregated metadata, not isolated incidents. By triangulating caller data with independent databases, the hub reveals credible red flags and evolving attacker tactics. One common objection—that data is noisy—is addressed: disciplined filtering and reproducible methods preserve signal integrity. Consequently, institutions can implement structured controls and continuous monitoring without stifling innovation, maintaining skepticism while advancing robust fraud detection across dynamic threat landscapes.







