Scam Awareness Research Hub Phone Number Lookup Scams Explaining Fraud Detection Queries

The Scam Awareness Research Hub aggregates findings on phone number lookup scams and the fraud-detection signals they trigger. It traces how detection queries reveal scam origins, evolution, and lifecycle stages, translating data into risk indicators for stakeholders. The approach emphasizes independent verification, red flags, and disciplined decision-making. It highlights how social engineering exploits contact data and how automated defenses might act without human prompting, leaving a question as to what comes next.
What Is Scam Awareness Research and Why It Matters
Scam awareness research aims to understand how individuals recognize and respond to fraudulent schemes, with the goal of reducing harm and improving protective interventions.
The field analyzes decision processes, defender behaviors, and system defenses to reveal how people detect threat patterns.
It documents scammy payoffs, deception cues, and red flags, while identifying authentication gaps that compromise security and informed choice.
How Phone Number Lookup Scams Work Today
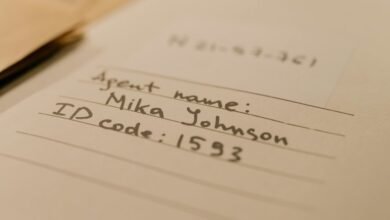
Phone number lookup scams exploit the ease of linking contact data with publicly available or stolen identifiers to harvest personal information or access accounts.
They rely on databases and social engineering to assemble profiles, enabling targeted phishing and credential theft.
The practice highlights vulnerabilities in caller identification systems, where techniques like caller spoofing undermine trust and complicate verification, enabling broader phone scams.
Fraud-Detection Queries: What They Reveal About Scams
Fraud-detection queries illuminate where scams originate and how they evolve, providing a structured lens to assess patterns, timing, and incident outcomes.
Fractions of data reveal fraud detection implications, guiding researchers toward root causes and lifecycle stages.
Carefully, the analysis interprets scam data signals, distinguishing noise from meaningful trends while maintaining methodological restraint and safeguarding against overreach in conclusions.
Practical Defenses: Spotting Red Flags and Protecting Yourself
In addressing practical defenses, the focus centers on clear, actionable indicators that individuals can use to evaluate unsolicited contacts and avoid missteps. The analysis highlights scam red flags and protective measures, emphasizing verification, independent contact methods, and fiscal caution. It notes fraud detection cues and risk assessment, translating scam insights into disciplined, autonomous choices to preserve autonomy and security.
Conclusion
The analysis demonstrates that phone number lookup scams deploy social engineering and data vulnerabilities to harvest trust and access. Fraud-detection queries reveal pattern shifts, timing anomalies, and cross-channel inconsistencies, enabling early risk signals when examined systematically. Caution and independent verification remain essential. Practitioners should translate these findings into automated safeguards and clear red flags, guiding prudent action. In sum, awareness acts as a shield, turning fragile data practices into a hardened defense—a careful, steady hand on the fuse.